Penetration Testing Services
At Pentest People, we offer industry-leading penetration testing services designed to identify and eliminate vulnerabilities in your systems, ensuring robust and reliable defences.
CHECK & CREST-Accredited: We have a range of CHECK & CREST accreditations for our excellence and expertise in penetration testing.
Innovative Vulnerability Platform: Access detailed reports and real-time data to understand and address security weaknesses promptly.
PTaaS Approach: Penetration Testing as a Service Model means you stay secure all year round with manual tests and automated scans



Why Use Pentest People For Your
Penetration Testing Services?

CREST Certified Penetration Testing Services
Our CREST certified professionals bring extensive experience across various sectors, ensuring accurate penetration testing and robust cyber defence.

Innovative Vulnerability Platform
Our platform offers real-time visibility, automated scans, and continuous monitoring for seamless and efficient vulnerability management.

Ongoing Vulnerability Scanning
Beyond testing, we offer continuous vulnerability monitoring to keep your business secure.

Live Reporting & Remediation Checks
Live reporting lets you fix issues in real-time, saving time and reducing risk. Remediation checks ensure vulnerabilities are removed for peace of mind.
Professional Penetration Testing Services From a Reliable Team
At Pentest People, our CREST-certified professionals offer comprehensive penetration testing across all aspects of your digital infrastructure. We combine automated tools with expert manual testing to identify vulnerabilities that automated scans often miss.
Our real-time reporting and actionable insights ensure you can address risks quickly and efficiently. With a focus on safeguarding your business, we help you meet compliance standards, protect critical data, and defend against evolving threats. Trust our reliable team to keep your organisation secure.
Trust us to keep your business secure with cutting-edge technology and expert insight, tailored to meet your specific needs.

1000’s of Organisations Trust Pentest People For Their Penetration Testing






























What is Penetration
Testing?
Penetration Testing, also known as pen testing or ethical hacking, is the process of testing networks, web applications, cloud environments and more to find security vulnerabilities that an attacker could exploit. A penetration test can be used to assess the security of a system and identify any potential weak points that could be exploited by malicious actors.
Penetration Testing can be used to simulate different types of attacks, including SQL injection, denial of service (DoS), and man-in-the-middle (MiTM) attacks. By attempting to exploit vulnerabilities, penetration testers can gauge the effectiveness of a company’s security measures and identify any areas that need improvement.

Talk to an Expert About Your Cyber Security Options
Fill out our contact form and a member of the team will be in touch to discuss your needs and offer support or contact is by phone on 0330 311 0990

Our Penetration Testing Methodology
Pentest People use a range of techniques from the 3 most widely used Pentesting methodologies; OSSTMM, OWASP & NIST. Visit our Penetration Testing Methodolgy page for a full breakdown.
The 6 main steps in any Test are:Initial Scoping, Reconnaissance,
Assessment, Reporting, Presentation and Remediation.

Six-Step Method
Our Penetration Testing Methodology
.webp)
Scoping & Intelligence Gathering
Our experts will listen to you and your needs to develop a tailored testing strategy. From here our consultants will use a wide variety of penetration testing tools and resources to gather information on your organisation.

Reconnaissance & Threat Modelling
After gathering enough information or consultants will develop an approach to testing your organisation, looking at 3 main factors; where are you most vulnerable, what are the best attack techniques for the job at hand and how can they deliver the test while safeguarding your business from any issues.

Vulnerability Analysis
In this phase, the defined targets are thoroughly scanned in order to uncover any existing vulnerabilities. This involves listening for open ports, identifying services that are running, and developing an attack plan based on the information collected from these scans.

Exploiting Your Systems
This stage is where our consultants see how far into your systems they can go using industry leading techniques, custom built tools and first-hand experience.

Determining Severity
After the consultant has a session running on a compromised machine they will determine the severity by seeing which assets and networks they can gain access to and how much information they can gather. This allows us to rank your vulnerabilities from low-critical in the SecurePortal

Reporting & Remediation
Now the test is complete our consultants will fill out a detailed report of their findings, broken down by category and type, adding any remediation advice to the exploits and vulnerabilities they discovered. This data will be accessible via SecurePortal and follow up calls will be made to walkthrough the test and the steps required to remove the risks found.
A Range of Testing Options
We have an array of Penetration Testing Services to suit all businesses

Infrastructure Penetration Testing
Assess and measure your cyber security through Infrastructure Testing to allow you to manage the identified issues.

Web Application Penetration Testing
Assess your critical Web Applications for Security Vulnerabilities with our Web Application Testing Service.

Cloud Penetration Testing
We offer a range of cloud services to highlight areas of misconfiguration and risk in your AWS & Microsoft instances.

Mobile Application Testing
Let Pentest People perform a thorough test on your mobile applications for both IOS & Android operating systems.

CREST OVS Web App Assesment
Let Pentest People Assess your Web Applications to the all new CREST security standard.

Cyber Essentials & CE+
Guard against the most common cyber-security threats and demonstrate your commitment to cyber-security by becoming Cyber Essentials Accreditation.

IT Health Check
Pentest People are a CHECK accredited organisation and can scope and perform your IT Health Check (ITHC) for access to the Public Services Network (PSN).

API Penetration Testing
Let Pentest People assess your API for Security Vulnerabilities with a thorough API Penetration Test.

Desktop Application Testing
We offer robust and reliable solutions, meticulously designed to ensure your application's optimal performance.

Red Team Assessments
We offer Red Team Assessments, to simulate a realistic scenario from an Advanced Persistence Threat (APT) group’s perspective. Highlighting all vulnerabilities from a range of vectors.

Social Engineering
Let Pentest People research, develop and manage a Social Engineering assessment of the security of your people and processes utilising the latest techniques.

IoT Penetration Testing
At Pentest People our IoT testing services offer a crucial means to evaluate and strengthen the security measures associated with any given connected device. Experience peace of mind knowing your IoT devices are fortified against potential threats.
You Can Trust in Pentest People to Deliver Industry Leading Testing
.webp)




Why Penetration Testing is Essential for Your Business
As cyber threats are becoming more sophisticated, Penetration Testing is becoming a must for all businesses, its crucial for identifying and mitigating security vulnerabilities before malicious actors can exploit them. Regular penetration testing helps businesses to:
- Protect Sensitive Data: Safeguard your valuable data from breaches and unauthorised access.
- Maintain Compliance: Ensure adherence to industry regulations and standards, avoiding hefty fines and legal repercussions.
- Enhance Security Posture: Continuously improve your defences against evolving threats.
- Build Trust: Demonstrate to clients and stakeholders that you take cybersecurity seriously, boosting your reputation and trustworthiness.

What Should a Penetration
Test Tell You?
A Penetration Test should provide you with a comprehensive understanding of your system's vulnerabilities and the potential impacts they might have on your business. At Pentest People, we believe in going a step further. We don't just identify security gaps; we offer clear, actionable remediation advice via our SecurePortal.
Our team of experts presents their findings in a straightforward,
easy-to-understand manner, outlining practical steps to enhance your security posture. We're committed to making the process of penetration testing as smooth and beneficial for you as possible.

What Sort of Systems Should be Tested?
When it comes to cyber security, no system or application should be left unchecked. From your network infrastructure and web applications to mobile apps and wireless systems, each component plays a crucial role in your business operations and thus, presents potential avenues for security breaches. It's also vital to consider cloud-based services and APIs, as these are increasingly common targets.
At Pentest People, we understand the diverse nature of today's digital ecosystems, which is why our penetration testing services encompass all these areas. Our team of experts utilizes cutting-edge methodologies to probe and test every aspect of your IT environment. With us, you can be confident that all potential vulnerabilities, across all systems and applications, are thoroughly examined and addressed. By choosing Pentest People, you're choosing comprehensive protection for your business in the digital age.

See What Our Clients Have to Say About our Professional Services
With GuardNest Testing Has Never Been Simpler.
Discover the power of our Innovative Vulnerability Platform, designed to revolutionise the way your IT team handles cyber security. Our platform offers an easier way to analyse and manage testing results with built-in comprehensive infrastructure and web application vulnerability scanning, delivering detailed digital reports that highlight every potential threat. Gain access to live expert remediation advice from our seasoned consultants, ensuring you have the guidance needed to tackle vulnerabilities effectively all from within the portal.
GET In Touch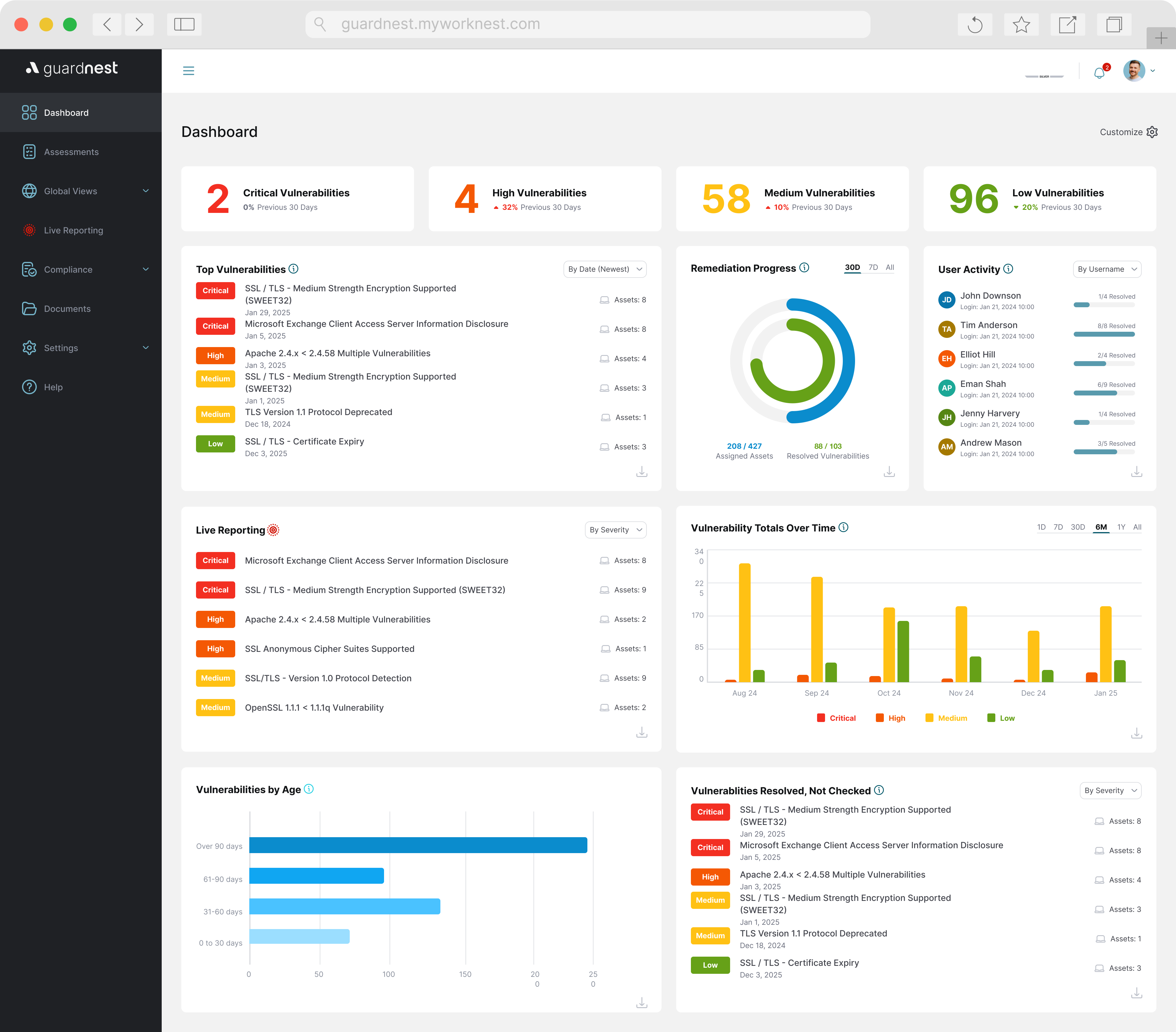
What Are You Waiting For? Get a Quote Today & Fortify Your Cyber Defences
With a range of Penetration Testing services, years of experience and award winning solutions, we know you and your team can rely on us to deliver comprehensive, thorough and professional testing.
We've developed our approach to Penetration Testing from client feedback and our own practical experience, reducing the burden on IT teams
post-test with SecurePortal and finding and fixing vulnerabilities quicker. If you want to find out more or get a quote, get in touch today and our team will be more than happy to help you.

Need More Info on Penetration Testing?
Frequently Asked Questions
How long does a penetration test take?
The duration of a penetration test can vary depending on several factors, including the scope and complexity of the system or network being assessed. On average, a penetration test can take anywhere from a few days to several weeks to complete.
How often should a penetration test be carried out?
In general, pentests should be conducted on a regular basis to ensure ongoing security. The specific frequency may vary, but annual pentests are often recommended as a minimum (we suggest a minimum of once every 6 months). However, certain situations may require more frequent assessments, such as after significant system changes or updates, implementation of new security controls, or prior to launching critical applications or systems.
How is a penetration test conducted?
A penetration test is conducted by a qualified professional who employs various techniques, tools, and methodologies to identify potential vulnerabilities and assess the effectiveness of existing security measures. The process includes gathering information, identifying targets, scanning for vulnerabilities, gaining unauthorised access, and documenting findings to provide recommendations for enhancing the system's security and safeguarding against potential threats.
Can a penetration test be performed remotely?
Absolutely, penetration tests can be performed remotely. At Pentest People, we utilise our innovative SecureGateway service, which allows us to conduct both external and internal penetration tests no matter where you are located.
Ou uses a small device known as a NUC or a VMWare Image. This technology enables us to create a secure connection between our testing environment and your internal network, ensuring a thorough and efficient penetration test, all without the need for our consultants to be physically present at your location.
What is Penetration Testing as a Service (PTaaS)?
Penetration Testing as a Service (PTaaS) is a comprehensive cybersecurity service offered by Pentest People, aimed at identifying vulnerabilities and assessing the security of a computer system, network, or software application. PTaaS involves conducting simulated attacks, penetration tests and ongoing scanning in order to proactively identify potential weaknesses and security gaps in order to strengthen the overall security posture. This service provides valuable insights and recommendations for remediation, helping organisations to protect their sensitive data and assets from potential threats.
What is the difference between a penetration test and a vulnerability scan?
The difference between a penetration test and a vulnerability scan is that a penetration test is a comprehensive assessment conducted by a skilled professional to actively exploit vulnerabilities in a system or network in order to identify potential security weaknesses and assess the effectiveness of current security measures. On the other hand, a vulnerability scan is a less intrusive and automated process that scans and identifies known vulnerabilities in a system or network, providing a report of potential weaknesses without actively exploiting them.
What is a Pen Test?
A Pen Test or Penetration Test is a security assessment conducted on a computer system, network, or application to identify vulnerabilities and weaknesses that could be exploited by unauthorised individuals. It involves simulating real-world attack scenarios to assess the system's capacity to withstand and defend against potential threats, providing valuable insights for improving security measures and safeguarding against cyberattacks.
.png)
















.svg)







.webp)

